This lab covered two critical data protection practices: securing data at rest through encryption and access controls, and validating backup and recovery procedures. The environment was an Ubuntu VM where LUKS encryption was applied to protect sensitive data even in the absence of full-disk encryption at install time.
Project Scope
- Protected sensitive data using restrictive file permissions and post-install LUKS encryption.
- Simulated a realistic remediation path for a system that was not encrypted during initial setup.
- Tested backup creation, data deletion, and successful restore to validate recovery readiness.
Impact
- Improved confidentiality by securing sensitive data both through permissions and encryption at rest.
- Reduced recovery risk by validating that backups could actually restore deleted data successfully.
- Demonstrated a practical security workflow that connects protection, resilience, and recovery.
Tools & Methods
- Ubuntu Linux
chmod- LUKS
cryptsetuptar- Command-line backup and restore validation
File Permissions
A secure_data directory was created and locked down with restrictive permissions, ensuring only the owning user could read, write, or execute within it:
mkdir secure_data
chmod 700 secure_data
LUKS Encryption
Since the VM was provisioned without full-disk encryption, an encrypted container was created post-install to house the secure_data directory. The process involved creating the container, formatting it with LUKS, opening it with a passphrase, mounting it as a filesystem, and migrating the secured data into it — simulating a realistic remediation scenario where encryption must be applied to an existing system.
Backup & Recovery
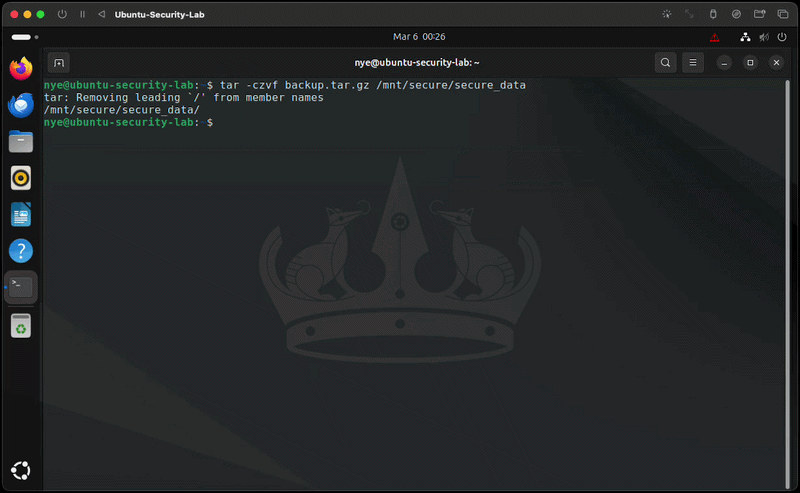
A compressed archive of the secured data was created using tar:
tar -czvf backup.tar.gz secure_data
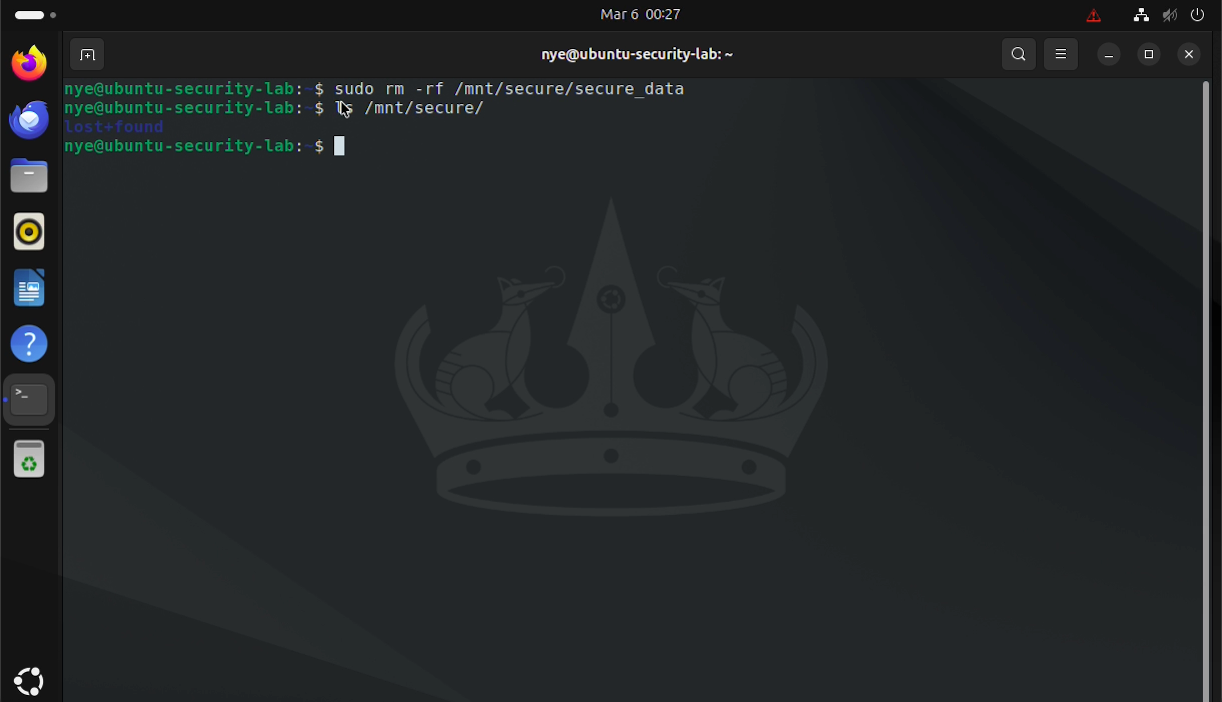
Data loss was then simulated by deleting the original directory, followed by a successful restore from the backup — confirming the integrity and reliability of the backup process.
Key Takeaways
Encryption at rest and tested backup procedures are non-negotiable in any production environment. This lab demonstrates the ability to apply LUKS encryption retroactively, enforce proper file permissions, and execute a reliable backup and recovery workflow — skills directly applicable to DevSecOps and systems security roles.